Within this post, we are going to explore a new tool that has recently been released, Netpicker.
Netpicker is a Python-based testing platform that makes it easy to ensure your network is running compliantly and securely. In this post, we will look at Netpicker's main features, some of the use cases it can solve, what you need to know to get started and how the Netpicker AI prompt can help you build your own tests.
Let's dive in!
What is Netpicker?
Netpicker is a tool for testing and validating your network to ensure that it is running as expected. At a high level, tests are created within Netpicker and scheduled to run periodically. The test results are stored in a database, which can then be queried to run compliance reports either via the Netpicker UI or the REST API.
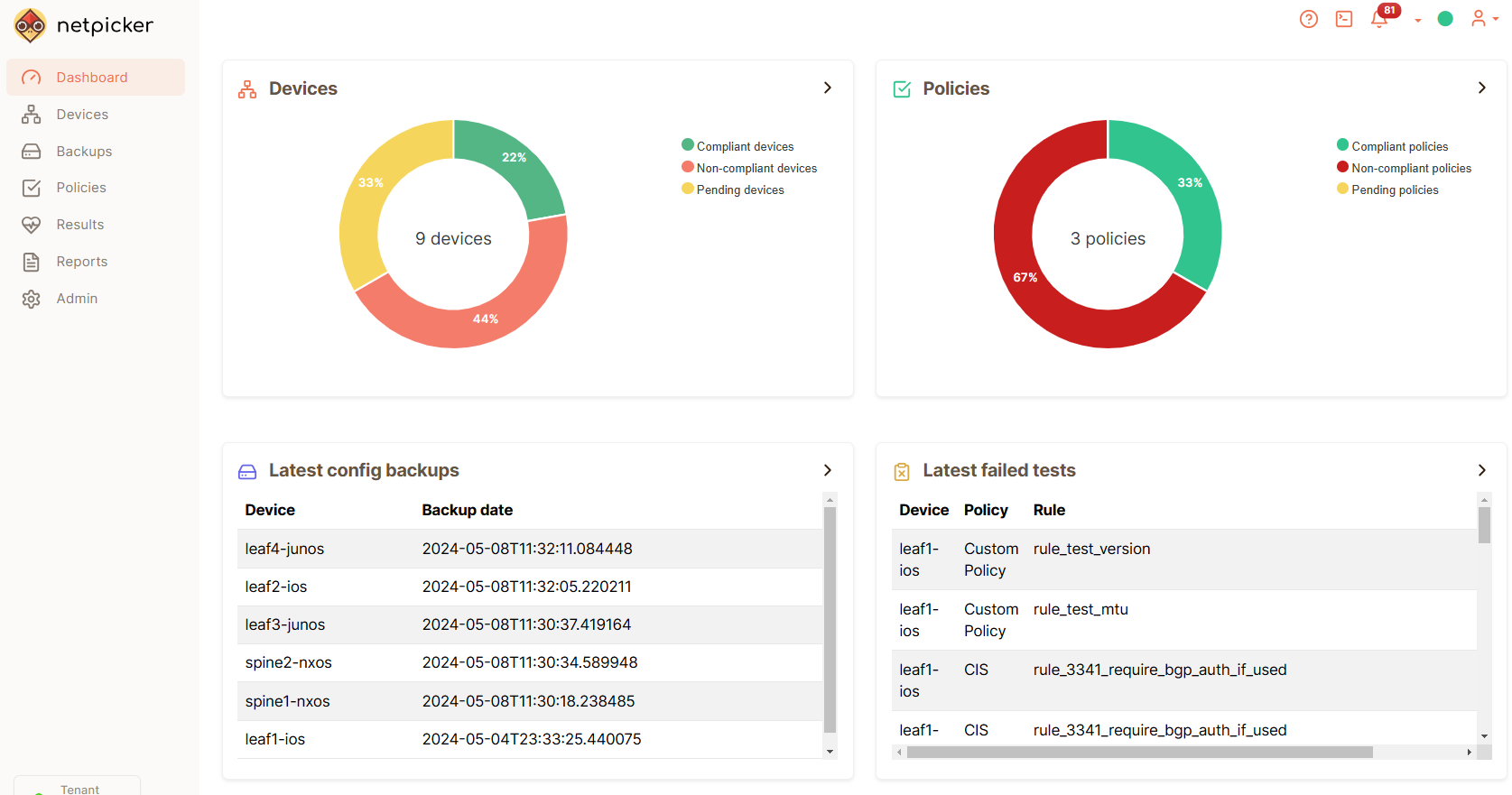
In addition to testing, Netpicker provides the ability to perform backups, which can be scheduled to run periodically.
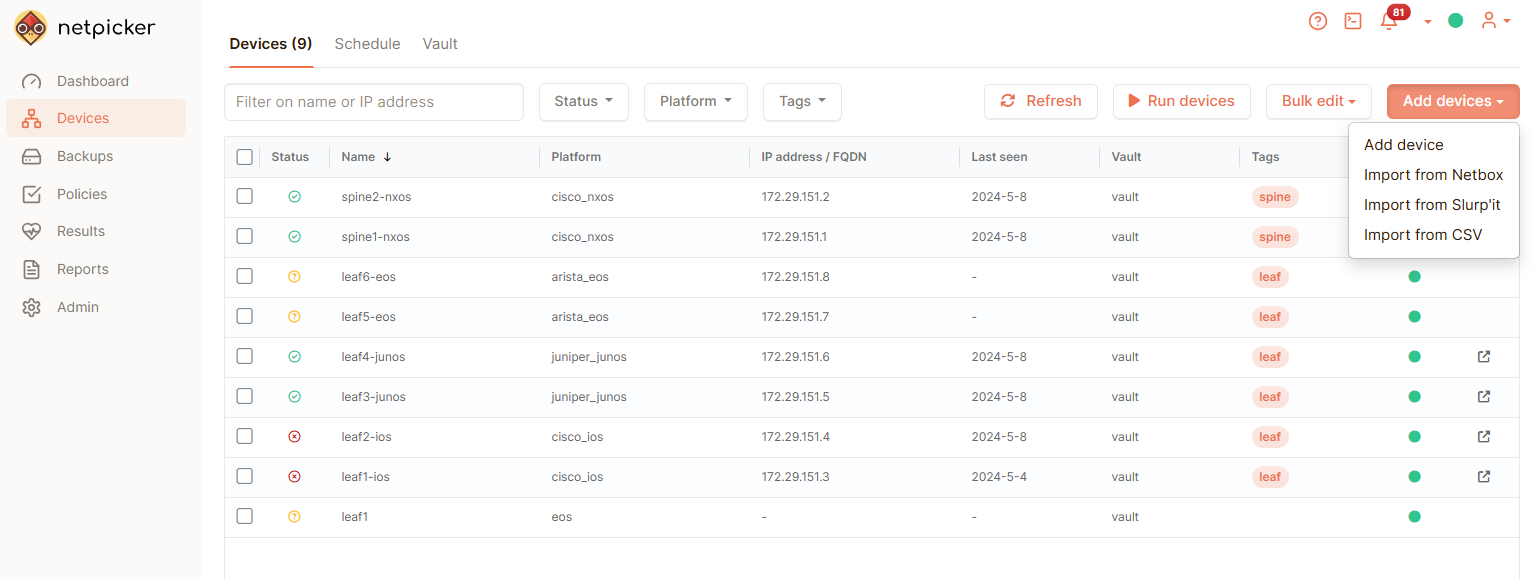
To allow Netpicker to collect data from your network, your devices and connectivity details (IPs, platform type, etc.) must be added to the Netpicker inventory. This can be done either via:
- Manual import
- CSV or API import
- Import from NetBox
- Import from Slurp`it
Under the hood, Netpicker leverages the open-source Python libraries - Netmiko and Pytest.
- Netmiko - For data collection. In order to connect out to the devices via SSH and run the required show commands. Due to Netmiko's large vendor support all of the vendors supported by Netmiko are also supported by Netpicker (at the time of writing, this is ~117).
- Pytest is used as the underlying testing framework. Tests can be written in Python. This provides huge flexibility when creating the tests and the test conditions.
It is worth noting that other Python libraries can also be used within the Netpicker tests such as pynetbox for working with data from a NetBox source of truth.
Netpicker Use-Cases
Netpicker lends itself to 2 main use cases. These are Config Backups and Compliance Reporting.
Config Backups
The ability to periodically backup device configurations. These backups can then be used to:
- Restore devices in the event of a failure
- Aid with troubleshooting to see what has changed over a period of time using Netpickers backup comparison feature.
By performing config backups within Netpicker provides a great enterprise-grade, free alternative to existing or older backup tools, such as Rancid or Oxidized.
Compliance
Creating compliance reports via the UI based on the results from the scheduled tests and device backups. This is extremely useful, especially when it comes to large networks. It allows us to visualise any issues relating to the network, design, security, or operations. For example, our compliance report can address questions such as:
- Which devices in my network are exposed to a given vulnerability?
- Show me the devices that do not conform to the network design policy of Y.
With these insights, the relevant remediation can be performed to ensure the network is updated to a compliant state.
Installing Netpicker
To install Netpicker you can choose to deploy it as a VM via their OVA image or a containerized deployment by using their Docker images. Both can be obtained using the link below:

Once you`ve installed Netpicker, a UI will be made available. Once logged in you can step through the required steps to add your devices. Either manually or via CSV, NetBox or Slurpit. You can also create a Vault to store your device credentials that will be used by Netpicker at the point it connects to your network devices.
Netpicker Features
With Netpicker up and running, there are some key features we can use:
Rules
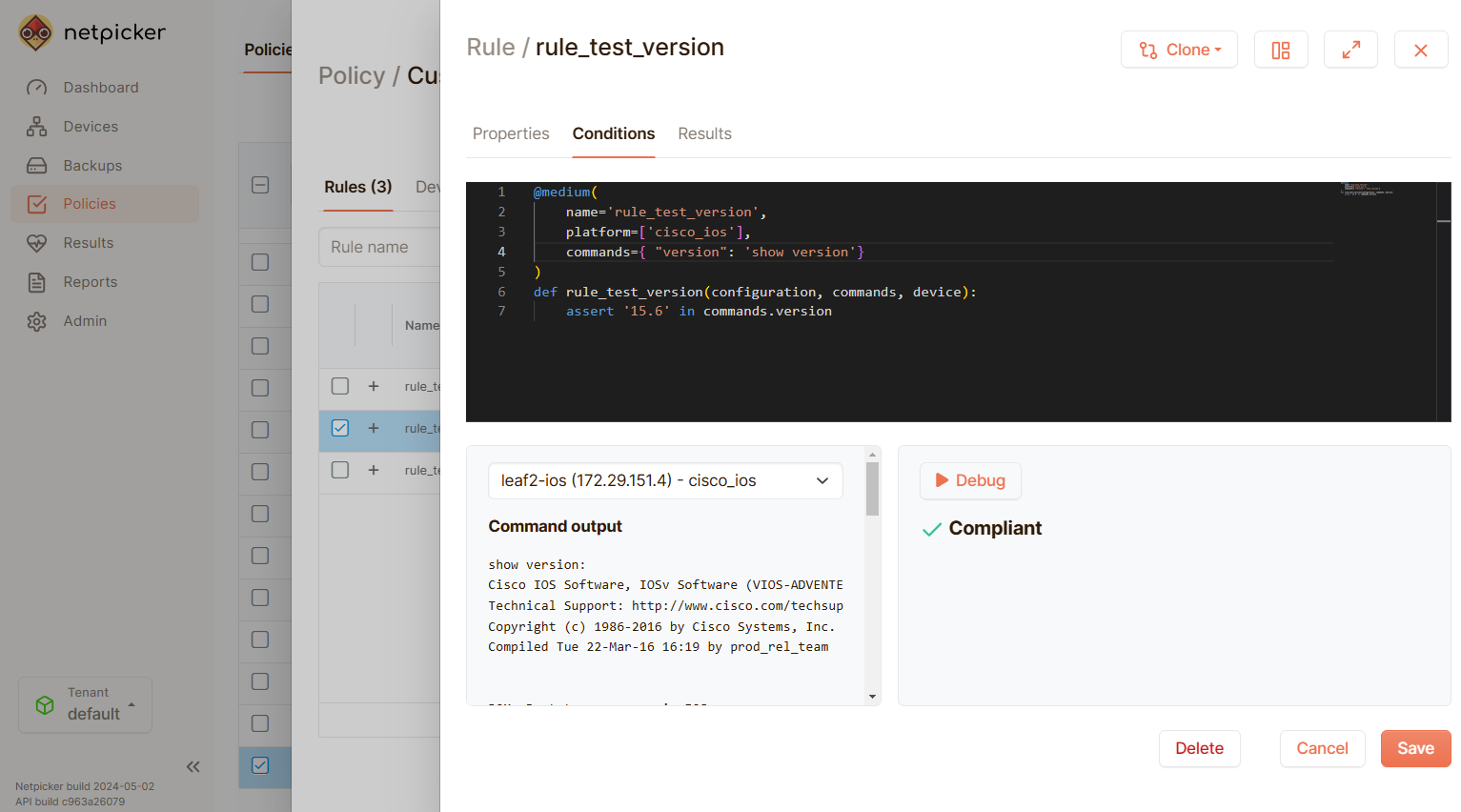
Within Netpicker, tests are created as Rules, and each rule is grouped within a Policy. These Rules are built using Python from the UI.
A number of pre-built rules are provided to test against CIS benchmarks and CVE vulnerabilities (example shown below). Note: These rules can also be located over at: https://github.com/netpicker/pytests-for-networking.
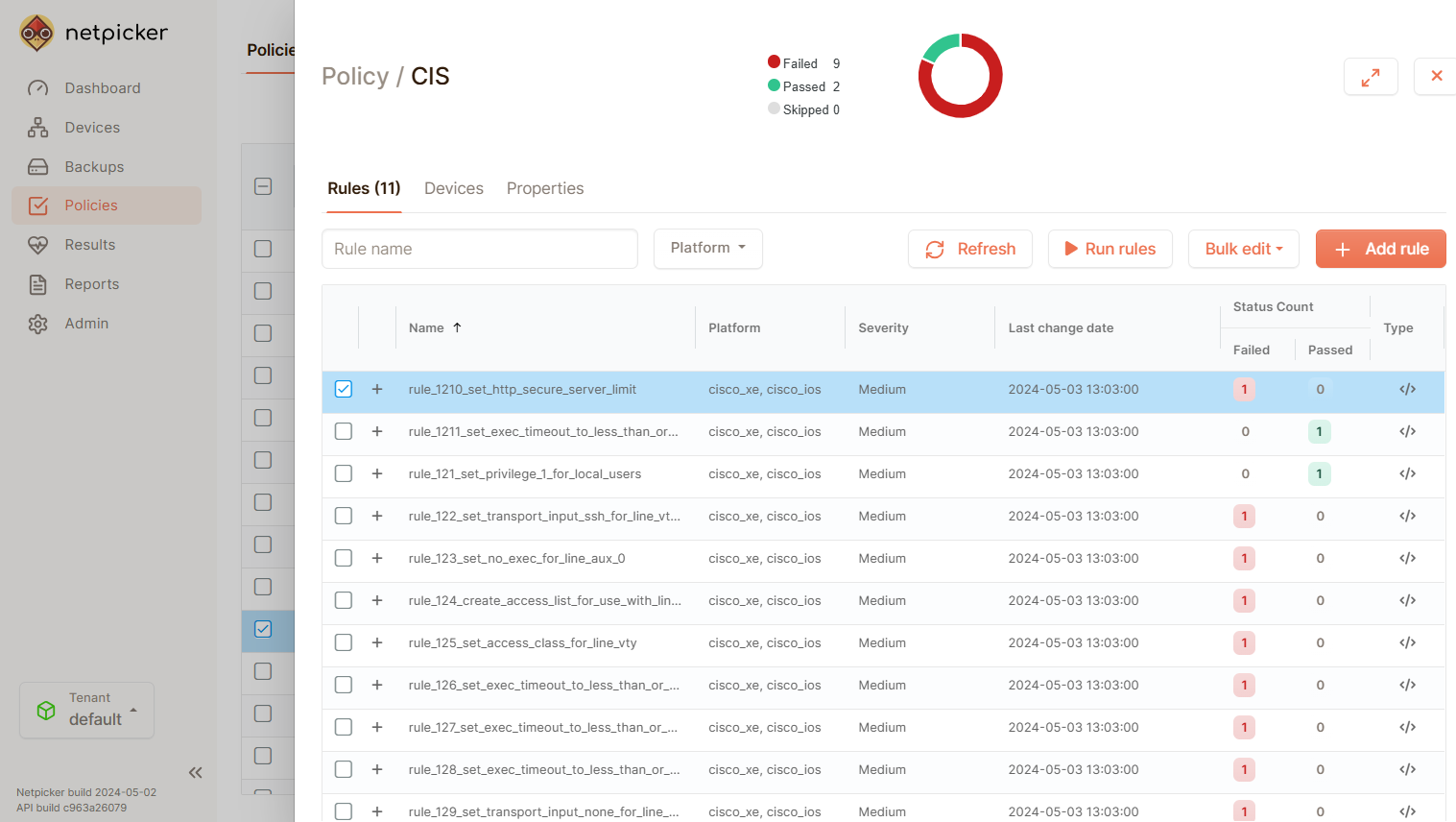
As we previously mentioned, the underlying testing framework that Netpicker uses is Pytest. Therefore, tests are created using Python (example shown below) and the Python assert keyword.
What is Python Assert?
Python assert is a built-in keyword that tests if a condition is True. If the condition is not True Python raises an error called an Exception. Testing frameworks, such as Pytest, then run the tests, looking for any Exceptions raised. Should an Exception be found, it marks the test as failed.
For example:
>>> assert 1 == 1
# True
>>> assert 1 == 2
# AssertionError is raised
For the assert keyword, we need data. Therefore, we can use data from a few different sources and formats:
Configuration - We can use the device configuration by passing in the configuration parameter to the test.
Commands - Use the output of any pre-fetched show command by using the commands dictionary
Device Data - We can use data properties from the device, like the name and IP address using the device property. Also, you can use real-time command output with the device.cli("show command here") method.
TextFSM - We can use structured data using prebuilt TextFSM templates by using the fsm attribute for any command provided. For example: commands.version.fsm.
NetBox - We can use NetBox data (expected state) by passing netbox to our test.
Slurp'it - We can also use Slurp'it data in our test either via API or via its SDK.
Below is an example of testing the MTU of our devices is 1500:
@medium(
name='rule_test_mtu',
platform=['cisco_ios'],
commands={"interfaces": "show interfaces"}
)
def rule_test_mtu(configuration, commands, device):
for i in commands.interfaces.fsm:
mtu_value = i.get('mtu', 'unknown')
interface_name = i.get('interface', 'unknown')
assert mtu_value == '1500', (
f"Incorrect MTU Value: {interface_name} has MTU {mtu_value}, expected 1500."
)
Netpicker also provides a ChatGPT AI Netpicker Network Test Creator. That allows you to generate the code for the tests automatically by just providing the details of the test you would like to create.
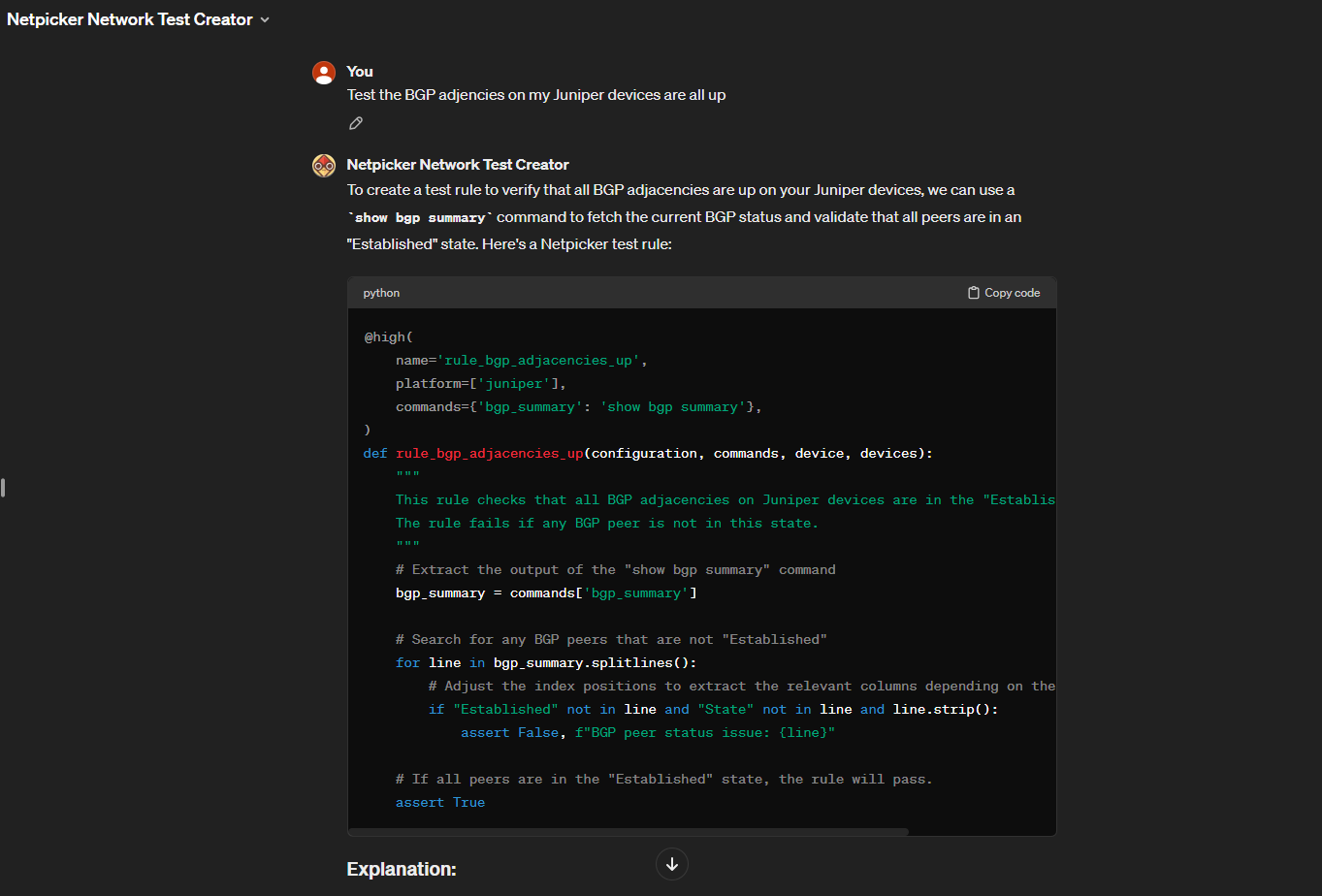
You can launch the Netpicker Network Test Creator using the link below:

Backups
Netpicker can schedule the backup of your device configurations. You can schedule this to run at a time of your choice.
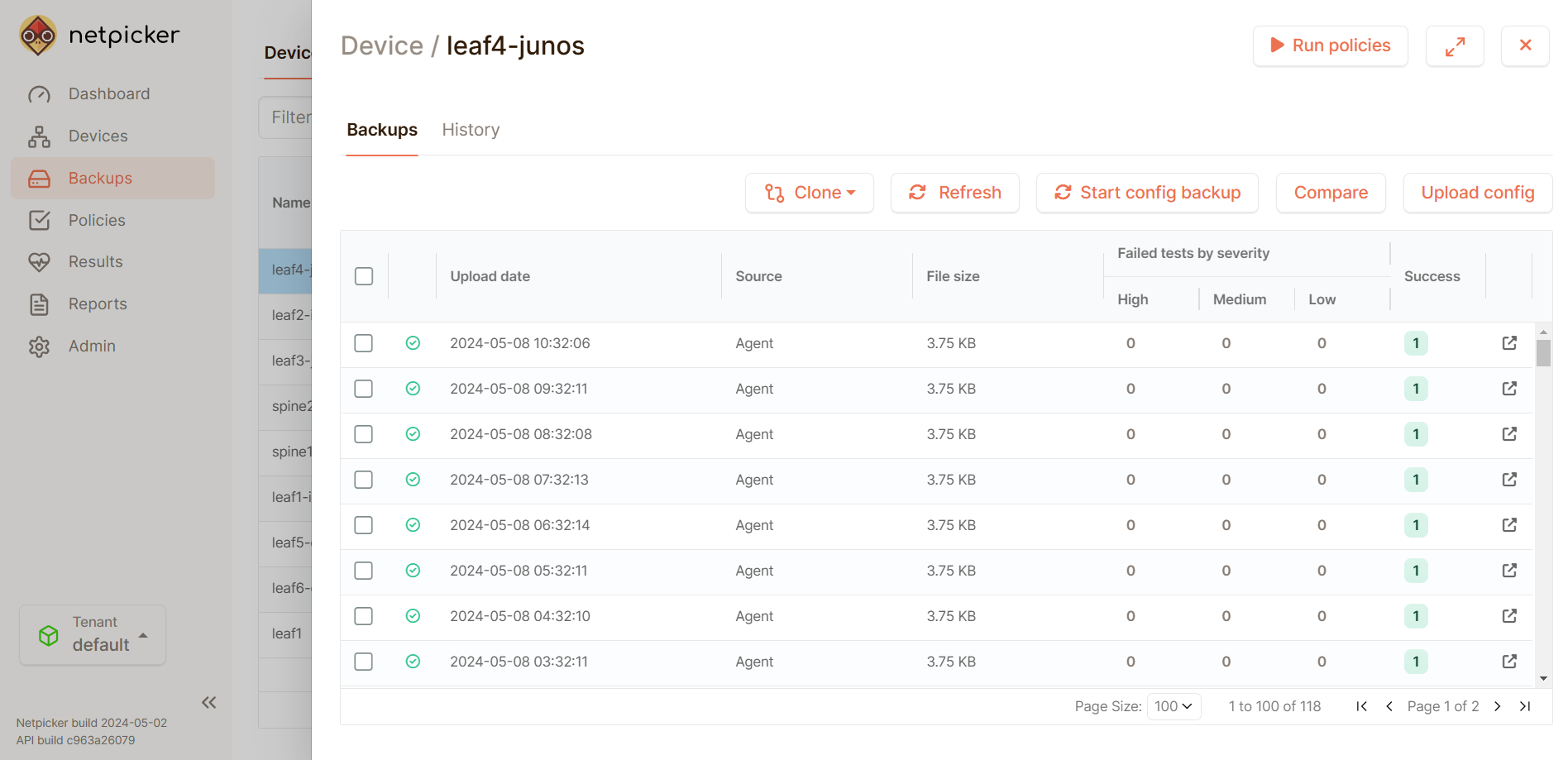
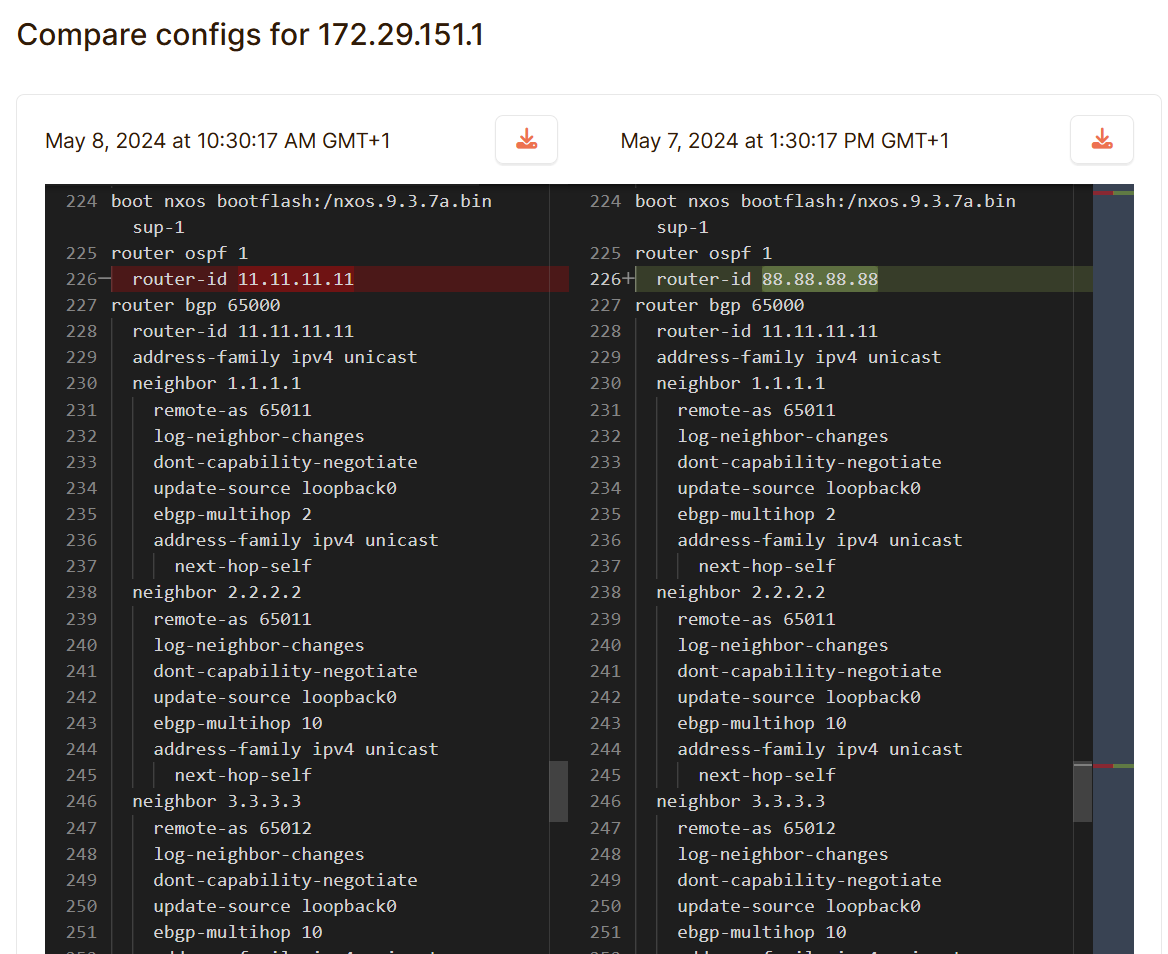
In addition, you can compare your configs to see the differences, which is extremely useful for troubleshooting.
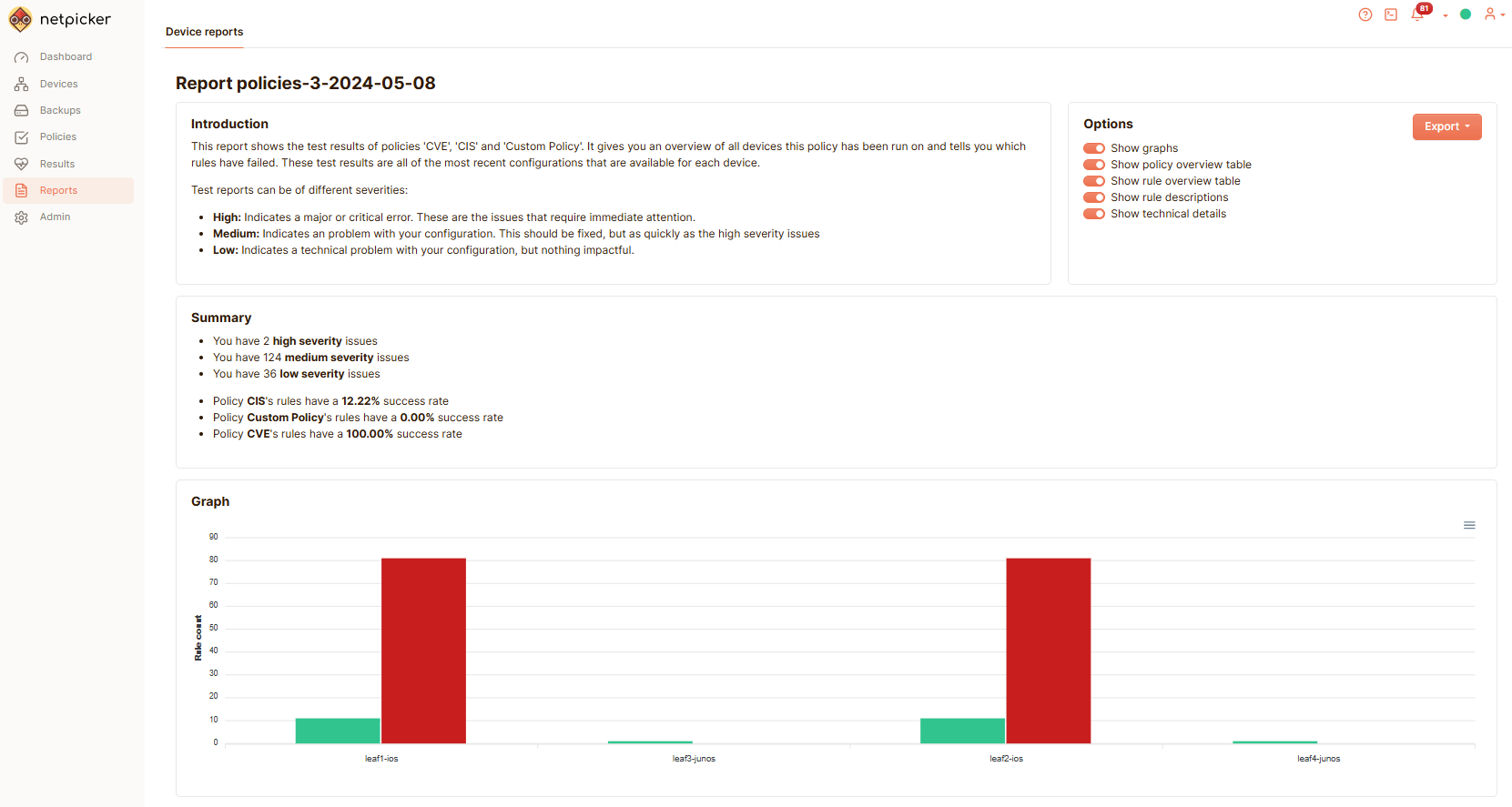
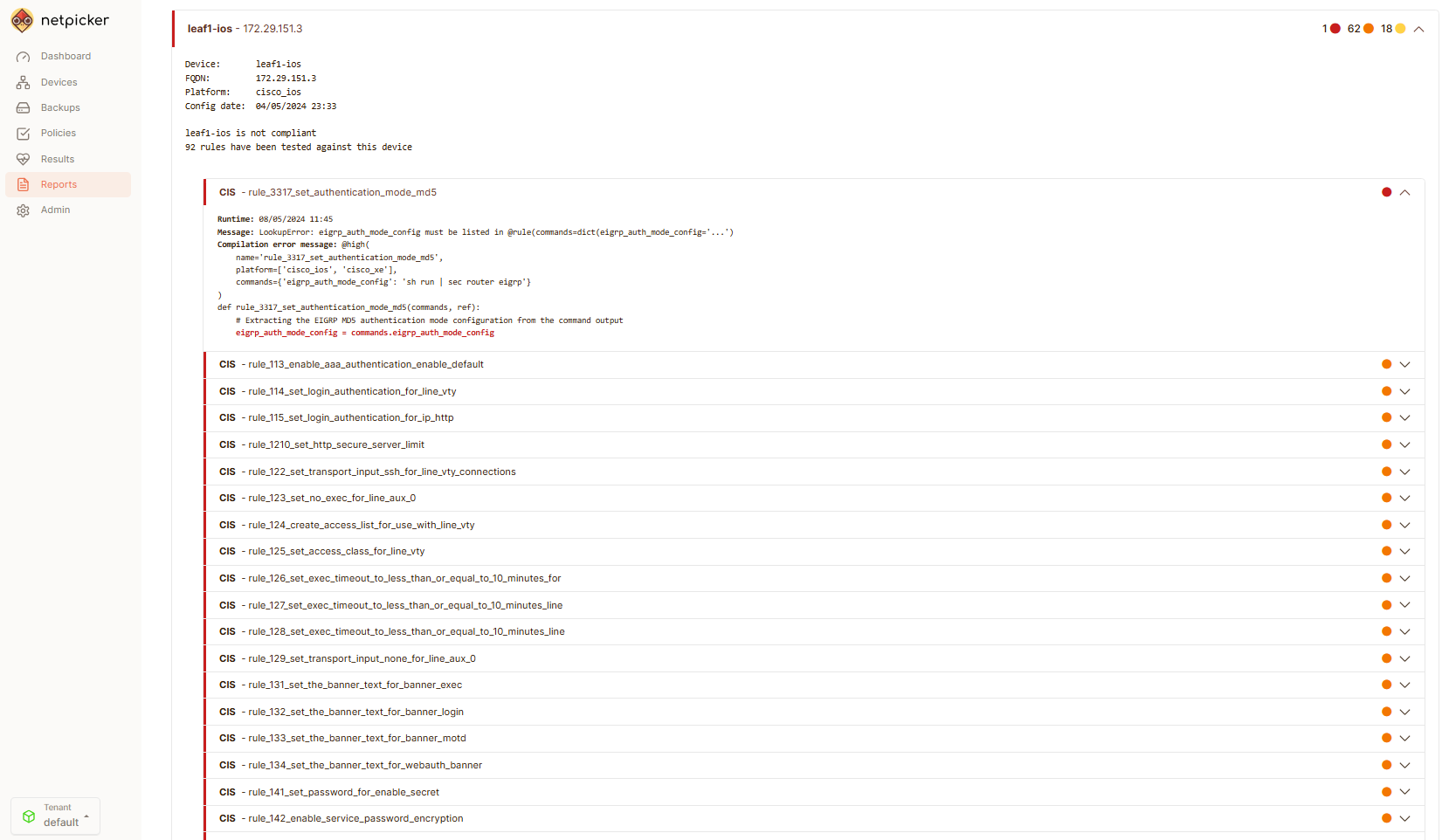
Reports
Netpicker allows you to build reports on the results of various policies and rules that run against your network. These reports can be viewed via the UI or exported as CSV or PDF.
The great thing about the reports is that they include visual graphs and also summarisation statistics, which help you see the "wood through the trees," especially in large networks.
Below are some examples of the graphing and summaries provided:
Summary
I hope you have enjoyed this introduction to Netpicker. As you can see, Netpicker bridges the gap between scheduling test execution and backups and getting meaningful data and insights using its reporting features.
This, coupled with its integration with NetBox and its ability to write tests using Python, makes it a great addition to any network automation stack.
Looking to Learn More?
If you want to learn more about Netpicker, the link below provides various resources, such as guides, a sandbox, and download links.